As part of World Passkey Day, Microsoft wants to send a specific message to all of us. That the password is no longer enough. And that we should switch to other authentication options.
Specifically, Microsoft security engineers are talking about and calling for the rapid adoption of passkeys. As online threats, the post writes, become increasingly automated, while AI is increasingly used in them, each account is only as secure as its weakest point.
Microsoft is stating something that we can all understand. That the real progress towards a stronger way to log in to accounts is to remove the details from those that can be phished.
Microsoft clarifies on its official blog that a password can easily fall victim to phishing and be intercepted. The most typical example is a fake page that imitates Outlook and invites you to enter your password.
The company says that if we manage to remove the password from the account, that is, an element that can be phished, and at the same time adopt secure methods to be able to recover this account in case of a problem, then we will have taken a real step towards real security.
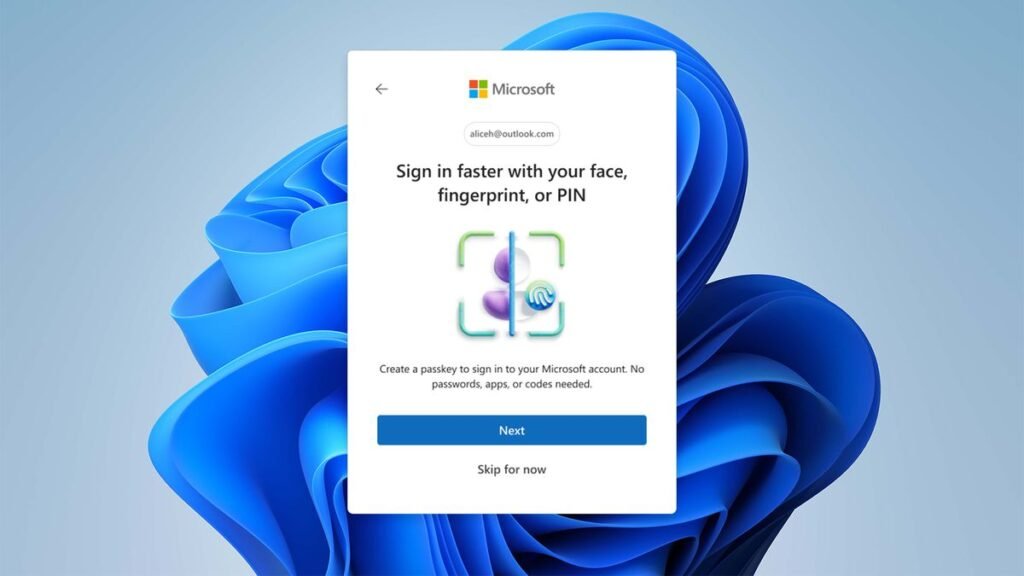
The solution to all this and the process by which it will be done is the passkey. The means of removing the password.
Product updates across sign-in and recovery
Across Microsoft, we’ve been steadily building passkey support into every layer of the identity experience from consumer accounts to enterprise access with Microsoft Entra, and from device-based authentication like Windows Hello to Microsoft’s password manager. This work ensures people can create and use passkeys wherever they sign in, with a consistent, phishing-resistant experience across devices, apps, and environments.
To make passkeys more accessible, we’re expanding where and how people can use them:
- Synced passkeys and passkey profiles in Microsoft Entra ID make it easier to scale passwordless sign-in across diverse environments. We’re expanding flexibility in cloud passkey management, including support for larger and more complex policies, and transitioning tenants to a unified passkey profile model.
- Entra passkeys on Windows make it simple for users to create and use device-bound passkeys directly on personal or unmanaged Windows devices using Windows Hello, and will be generally available in late May 2026.
- Passkeys for Microsoft Entra External ID will be generally available late May 2026, so your customer-facing applications can offer a more seamless, consumer-grade sign-in experience.
- Passkey-preferred authentication in Microsoft Entra ID (preview) detects registered methods and prompts the strongest one first. If a passkey is registered, that’s what the user sees—immediately.
- On the consumer side, with Microsoft Password Manager, users can now save and sync passkeys across devices signed in with their Microsoft account, with support for iOS and Android rolling out soon through Microsoft Edge.
Account recovery also plays a critical role in maintaining the integrity of identity systems. Historically, it’s been vulnerable to cyberattackers who try to hijack the recovery process, for example by impersonating legitimate users and requesting new credentials.
Microsoft Entra ID account recovery, generally available today, strengthens security for recovery flows by enabling users to regain access to their accounts through a robust identity verification process. Users can regain access after losing all authentication methods by using government-issued ID and biometric face checks. At general availability, we are expanding our identity verification ecosystem with two new partners—1Kosmos and CLEAR1—joining our existing partners Au10tix, IDEMIA, and TrueCredential.
Removing phishable credentials from user accounts
Strengthening authentication is important, but reducing risk means eliminating phishable credentials entirely. Microsoft is continuing to phase out legacy methods and move users toward phishing-resistant authentication. Starting in January 2027, security questions will be removed as a password reset option in Microsoft Entra ID due to their susceptibility to guessing and social engineering.
The rationale is straightforward: improving strong methods while removing weak ones shrinks the attack surface.
This is increasingly urgent as AI agents act on behalf of users. If an identity is compromised, cyberattackers can leverage those agents to access systems, execute workflows, and operate within existing permissions. Organizations need to address this risk quickly.



